AI integrated throughout
Dedicated module on offensive and defensive AI, including OWASP LLM Top 10, prompt injection, deepfakes, anomaly detection, and MITRE ATLAS.

Professional training in ethical hacking, cybersecurity and artificial intelligence. A practical 60-hour path with live instruction, hands-on labs, cloud-native security, offensive and defensive AI, Red Team, Purple Team, incident response and digital forensics.
Cybersecurity continues to show one of the largest talent gaps in the technology industry. This program positions learners for high-demand roles by combining offensive security, defensive operations, AI security, cloud, DevSecOps, incident response, and executive communication.
The commercial brochure positions the program around the market gap, with references to global unfilled cybersecurity roles, the LATAM deficit, breach cost, and attack detection time.
Not a generic ethical hacking course. This is a modern CertQA 2.0 certification path focused on 2026 demand: AI, cloud-native security, Zero Trust, DevSecOps, supply chain, OT/ICS, threat hunting and forensics.
Cyber Ethical Hacking CertQA 2.0 combines live instruction, a controlled lab environment, updated tools, certification assessment, and a practical career path.
Dedicated module on offensive and defensive AI, including OWASP LLM Top 10, prompt injection, deepfakes, anomaly detection, and MITRE ATLAS.
AWS, Azure, GCP, Docker, Kubernetes, DevSecOps, CI/CD, IaC security, CSPM, and Zero Trust architecture under NIST SP 800-207.
Practical labs using tools such as Kali Linux, Nmap, Nuclei, Metasploit, BloodHound, Pacu, Burp Suite, Volatility 3, Ollama and more.
Official certification exam with 120 multiple-choice questions, 3-hour duration, passing score above 70%, and biometric proctoring.
Ethics, authorization, documentation, responsible disclosure, and regional legal context for cybersecurity practice in Latin America.
Includes executive reporting, FAIR framework, risk communication, and translating technical vulnerabilities into business impact.
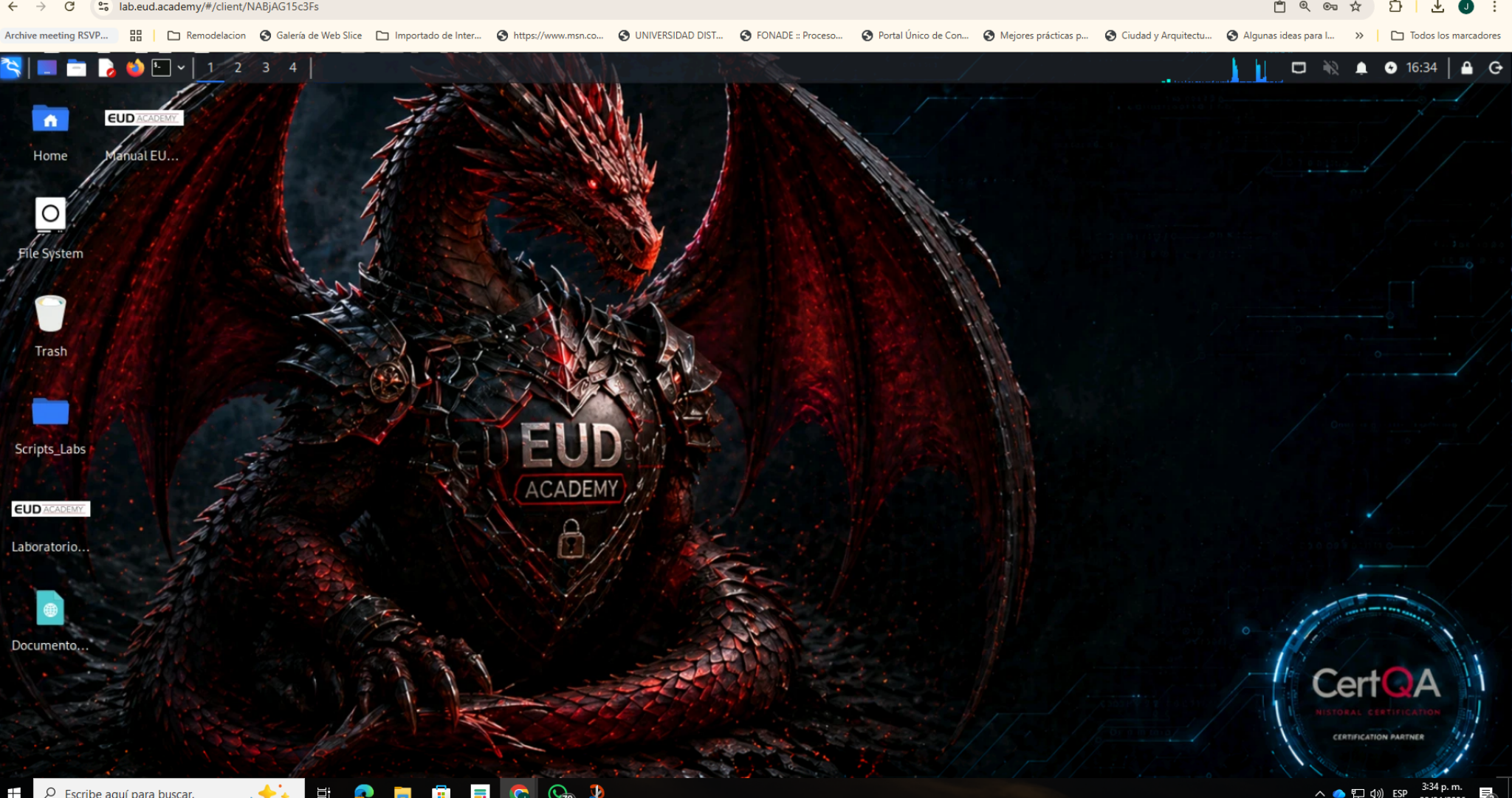
The lab access documentation shows a dedicated environment at lab.eud.academy, where each student connects through the browser to an assigned Kali Linux machine and uses a controlled target machine for course practices.
This platform approach reduces installation friction, standardizes the environment, protects the learning process, and reinforces responsible use of tools only inside authorized labs.
The program is structured as 60 hours across 15 live sessions, with a dense and practical format supported by autonomous student work between sessions.
Professional ethics, LATAM legal context, SOW/NDA/ROE, chain of custody, responsible disclosure and Bug Bounty.
Passive and active OSINT, Shodan, MITRE ATT&CK, Cyber Kill Chain, SpiderFoot and AI-assisted correlation.
Nmap NSE, Nuclei, CVSS v4.0, EPSS, MISP, OpenCTI, Wireshark and JA3 fingerprinting.
Metasploit, Active Directory, OWASP Top 10 2025, API Security, C2 frameworks and Purple Team.
AWS, Azure, GCP, Docker, Kubernetes, CI/CD security, IaC, CSPM and NIST Zero Trust Architecture.
OWASP LLM Top 10, prompt injection, deepfakes, ML anomaly detection, UEBA, and MITRE ATLAS.
OWASP IoT Top 10, Binwalk, Modbus, DNP3, OPC UA, SBOM, Syft, Grype, SolarWinds and XZ Utils.
NIST SP 800-61 r3, ransomware response, tabletop exercises, ELK, Volatility 3 and cloud forensics.
Certification roadmap, LATAM market, C-Suite communication, FAIR framework and CertQA exam preparation.
The CertQA v2.0 certification evaluates eight domains across ethical hacking fundamentals, OSINT, vulnerability analysis, pentesting, cloud, DevSecOps, AI security, OT/ICS, supply chain, incident response, threat hunting, forensics, tools and best practices.
The exam includes biometric identity control and proctoring through the CertQA platform.
Graduates develop competencies across ethical hacking, Red Team, Purple Team, cloud security, AI security, DevSecOps, IR, forensics, OT/ICS and supply chain.
Plan and execute authorized security testing under professional ethical and legal frameworks.
Identify misconfigurations and security weaknesses in modern cloud-native environments.
Support detection, incident response, threat hunting and forensic analysis processes.
This program must be positioned strictly as ethical and authorized cybersecurity training. All tools and techniques are for controlled lab environments, authorized assessments, compliance, defense, and professional security improvement.
Cyber Ethical Hacking CertQA 2.0 offers a complete pathway: live training, hands-on labs, exam simulation, official certification and a professional roadmap for cybersecurity careers.